Sauna
Sauna is an easy difficulty Windows box. The box involves enumerating a webpage to get possible user accounts, check for weak accounts that are ASREPRoast-able, then further enumerating the box to get access to an account that has privileges to perform a DCSync attack.
While the box is considered “easy”, it contained a lot of methods for enumeration and exploitation that I don't have experience or plain was not aware of so it took a lot more time than expected. I learned a lot of new techniques, and for that I am happy.
A small note about this writeup: I did the majority of this box in January but stepped away from it for several weeks before wrapping it up recently. Due to the break in time, this writeup is not as verbose as I would typically want and does not contain as many screen captures as it should.
Contents
- Tools Used
- nmap scan
- Initial Enumeration
- Getting Remote Access
- Lateral Movement and Privilege Escalation
- Lessons Learned
Tools Used
nmap – Network mapping tool, used to enumerate a device.
enum4linux-ng – A tool for enumerating Windows computers through LDAP and RPC queries.
rpcclient – A tool for enumerating MS-RPC on Linux.
evil-winrm – A shell to interact with the WinRM protocol originally, but now works with PSRP, the PowerShell equivalent.
ffuf – A tool for web fuzzing, primarily used for enumeration of webpages.
impacket – A collection of tools, although I specifically used getnpusers, psexec, and secretsdump, which allows you to maliciously interact with a Windows system.
ldapsearch – A tool developed by the team that developed LDAPv3 at the Internet Engineering Task Force (IETF).
username-anarchy – A tool for generating usernames based on providing key information that commonly makes up usernames.
nmap scan
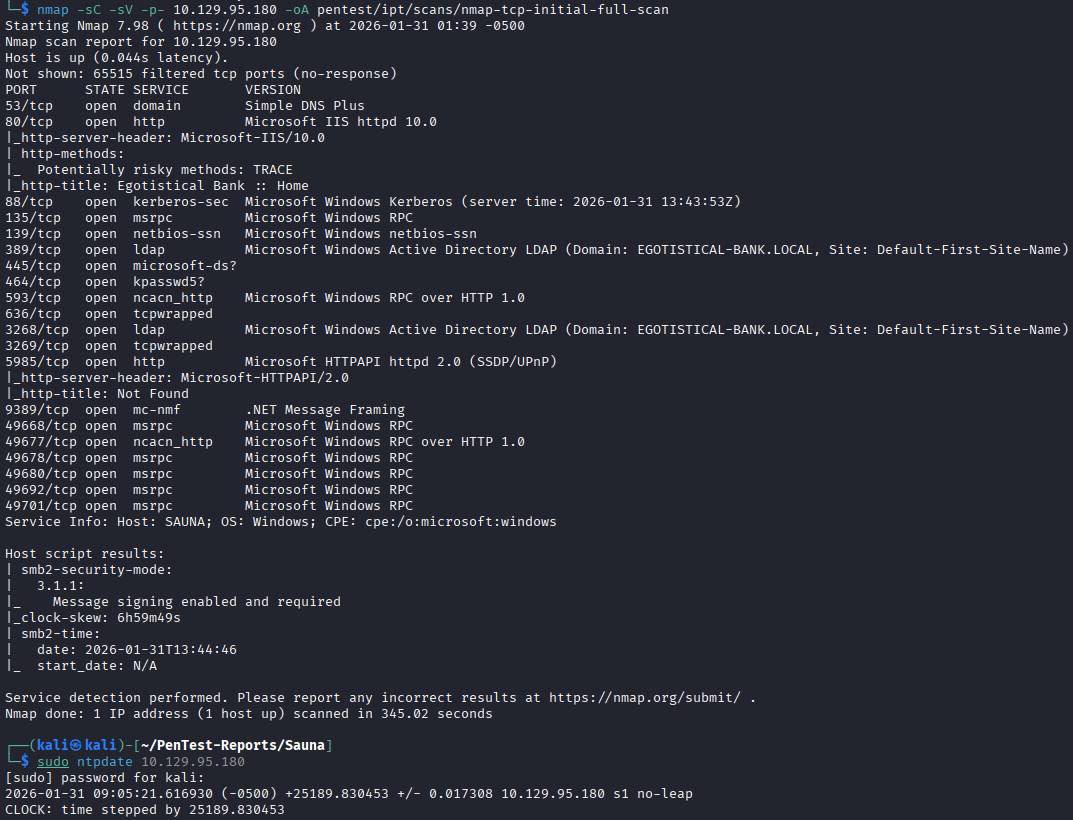
The initial nmap scan shows a Windows machine with LDAP, Kerberos, WinRM, and other Windows Active Directory (AD) ports. The only thing unusual that sticks out is that it is listening on port 80, which is typically associated with HTTP. The device is part of the domain EGOTISTICAL-BANK.LOCAL. After identifying that this box utilizes Kerberos, I synchronize my clock to the target's.
Initial Enumeration
My first target for enumeration is the SMB shares, but it looks like the Guest account is disabled, so I am not able to authenticate to any of the shares.
While checking the SMB shares, netexec states that null auth is enabled. Null auth is an anonymous session for authentication, similar to Guest but significantly more limited. This null auth session does not allow us to enumerate shares or anything via RPC.
The null auth does allow us to query LDAP without providing any credentials, so I run ldapsearch to try to enumerate some usernames.
ldapsearch -H ldap://10.129.95.180 -x -b 'DC=EGOTISTICAL-BANK,DC=LOCAL'
The -x switch here specifies basic authentication, but without providing any credentials it uses null authentication.
From the ldapsearch queries I run, I can see the password policy, which indicates there is no lockout threshold. I do also see an object with the common name 'Hugo Smith'; however, this is not a user object so I'm not sure what it is or what we can do with it.
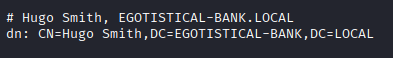
So we cannot enumerate users with this null session, and this “Hugo Smith” object sounds like a user, but I am not sure how to abuse it.
After hitting a wall here, I start enumerating the HTTP server which seems to be hosting a website. The website is some kind of financial website for a bank, and it contains some contact forms that I try to see if they are inject-able, but I do not have any luck. I use ffuf to try finding other pages or VHOSTS, but find seemingly relevant.
I don't find any easy exploitations on the webpage so I check the “guided mode” and it asks about a page where the employee names are present. I check around the website a bit more and in the about.html page it has a few employee names that we can add to a list. Once the list has been created, we run it through username-anarchy to create a list of likely usernames based on common naming conventions.
Unsure of what to do with this list of usernames, I check the “guided mode” again after some time and it recommends an ASREPRoast attack, which is something I had never heard of. Reading the netexec wiki it explains the attack as the following:
``` netexec wiki The ASREPRoast attack looks for users without Kerberos pre-authentication required. That means that anyone can send an ASREQ request to the KDC on behalf of any of those users, and receive an ASREP message. This last kind of message contains a chunk of data encrypted with the original user key, derived from its password. Then, by using this message, the user password could be cracked offline.
So in this attack, we can send an authentication request to the Kerberos server on behalf of another user who does not have pre-authentication required. The server will respond with an AS-REP response message that contains the TGT for the user, which we can then attempt to crack offline to get their password.
In our current position of not having any usernames enumerated, we can feed a list of usernames that we generated with `username-anarchy` to `impacket-getnpusers` to check for ASREPRoastable accounts.
The command user is:
```shell
impacket-GetNPUsers -request -format hashcat -dc-ip 10.129.95.180 'EGOTISTICAL-BANK.LOCAL/' -usersfile ./anarchy.list
This attempts every username generated to see if they have pre-athentication not required, then requests authentication on behalf of the account and returns the TGT. It seems like this uses the null session to query the accounts, but I'm not sure.
We get a hit when running this for an account fsmith.
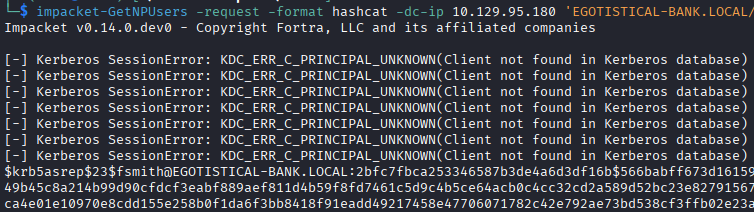
The output is the TGT in the form that hashcat can user, so I run the crack through hashcat and get the user's password while using the rockyou.txt list.
Getting Remote Access
With credentials to a user account, I begin enumerating services again as the authenticated user.
Its at this point that I step away for a few weeks, so this is where the writeup will be less verbose and only contain the path to root.
I get remote access with WinRM via evil-winrm and begin enumerating the box. I run SharpHound and winPEAS on the box and process the results.
SharpHound shows that there is an account, svc_loanmanager, that has privileges over the domain that allows a DCSync attack. That makes the account a high priority target.
Lateral Movement and Privilege Escalation
While reviewing the winPEAS output, I see that the same account, svc_loanmanager, is configured for autologon and winPEAS provides the credentials for the account. When an account is configured for AutoLogon, the credentials are stored in a registry key that in this case is accessible to us, so we can get the plaintext password.
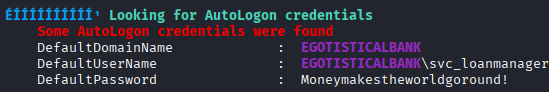
If you want to see what is being enumerated in the registry, you can run this command while connected to the machine:
reg query "HKLM\SOFTWARE\Microsoft\Windows NT\Currentversion\Winlogon"
With the password in hand, I carry out the DCSync attack using impacket-secretsdump which provides me the hashes of all the accounts in the domain, login as Administrator and grab the root flag. Its worth noting here, the dump includes LM hashes, not NT hashes, so in order to login with the Administrator LM hash, you need to use impacket-psexec, as evil-winrm requires the NT hash.
Lessons Learned
The biggest lesson to me here was learning about the ASREPRoast attack. Checking for this type of attack will be a major thing I look for in future boxes. I will also start using the technique here of creating a list of possible accounts with username-anarchy with names listed on a website. While the privilege escalation path on this box was very easy (with SharpHound), getting initial access was challenging for me.